scp the usage of pem record
I used to be requested easy methods to switch recordsdata the usage of scp with out a password the usage of a pem record for authentication. After studying this educational, you’ll know the way to generate an SSH key and convert it to a pem record to obtain or add recordsdata the usage of the scp command.
If you have already got your .pem key, you’ll be able to bounce to the Using scp with pem segment.
Generate a pem key for scp:
To start, let’s generate the ssh key pair via working the command beneath.
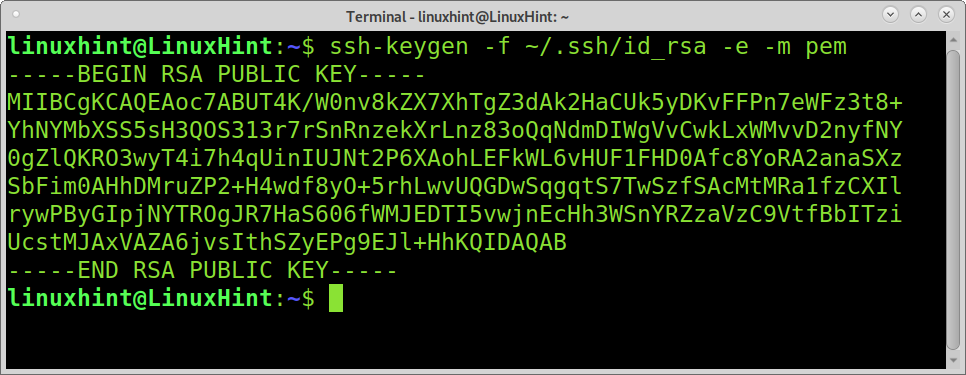
Execute the next command to create the .pem record.
ssh-keygen -f ~/.ssh/id_rsa -e -m pem
Once created the important thing pair, replica the general public key to the server you need to hook up with the usage of a pem record for authentication via working the command beneath. Replace the username “kali” together with your username and the IP cope with together with your server IP.
ssh-copy-id kali@192.168.1.100
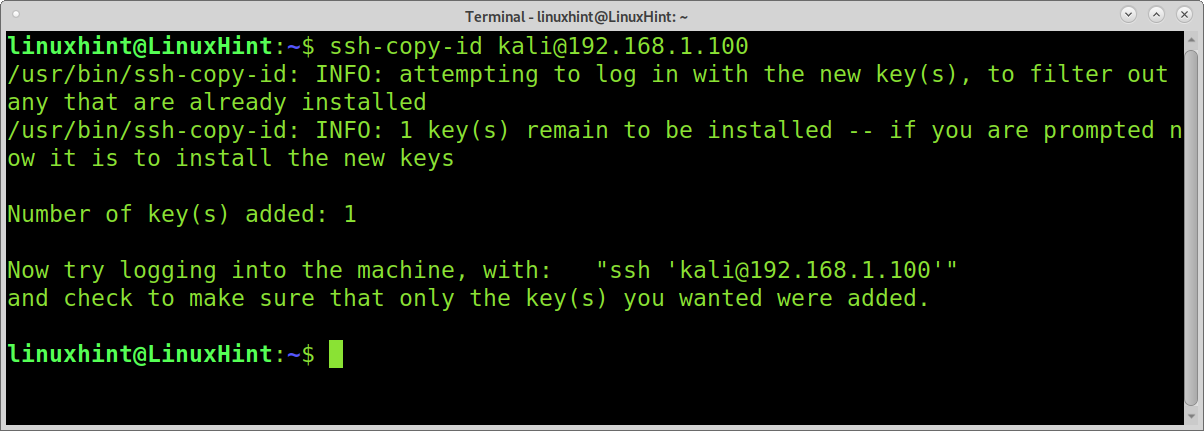
After working the command above, a record named pk_dsa.pem will have to be created inside of your own home .ssh listing.
Now you are prepared to obtain and add recordsdata with scp the usage of a pem record.
Upload record or listing the usage of scp with pem:
To use the scp command with a key pair, you want to put in force the -i (Identify record) flag.
In the primary instance, I display easy methods to add a record named linuxhintsignal to the server 192.168.1.100.
As you’ll be able to see within the symbol beneath, the scp command is adopted via the -i flag and the pem record named pk_dsa.pem. Then the record to ship is specified, adopted via the far flung username and server. The ultimate colon after the IP defines the default trail, which is the kali person house because the vacation spot listing.
scp -i pk_dsa.pem linuxhintsignal kali@192.168.1.100:
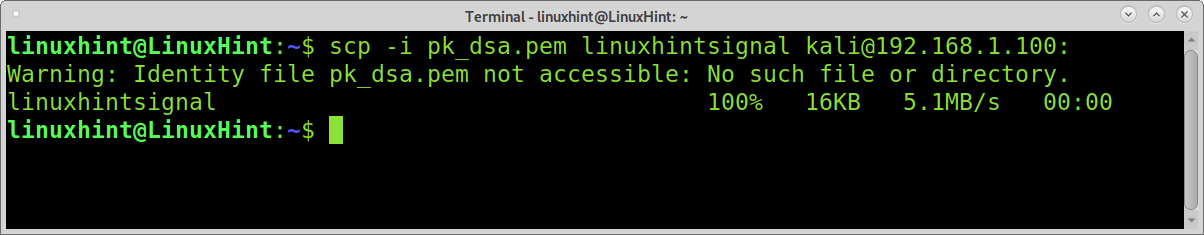
As you’ll be able to see, the record used to be uploaded correctly throughout the far flung person’s house listing (kali).
The following instance displays easy methods to add a listing (named listing) to the subdirectory named dir, positioned within the far flung house of the person kali.
As you’ll be able to see, to add directories recursively, you want so as to add the -r flag.
NOTE: I were given an error I solved when looking to seize this case via specifying the .pem trail (.ssh/pk_dsa.pem) as proven within the instance beneath.
scp -r -i .ssh/pk_dsa.pem listing kali@192.168.1.112:dir
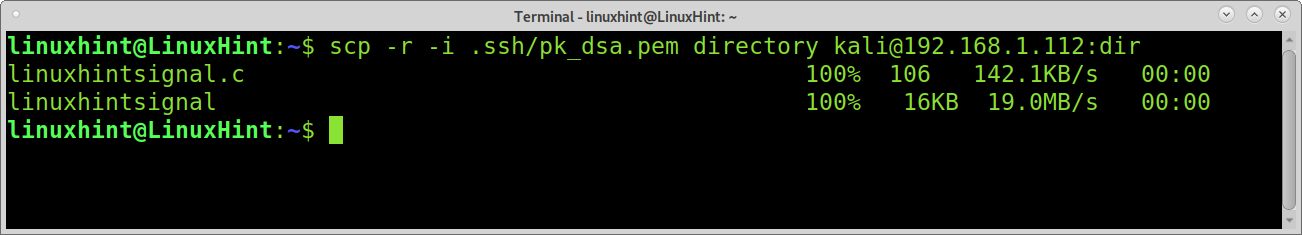
The listing is now below the objective’s dir subdirectory.
Download record or listing the usage of scp with pem:
In the former instance, the vacation spot listing used to be outlined on the finish of the command. The vacation spot listing will have to even be outlined on the finish of the command when downloading recordsdata, as proven within the following instance. This is as a result of scp used to be designed to be identical as conceivable to the common cp command.
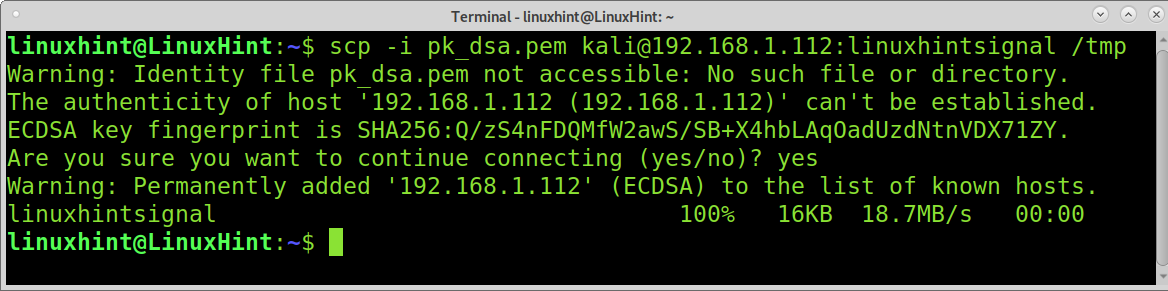
In the next instance, the record linuxhintsignal is downloaded to the native /tmp listing outlined on the command’s finish.
scp -i pk_dsa.pem kali@192.168.1.112:linuxhintsignal /tmp
Downloading a listing recursively additionally calls for the -r flag. The dir far flung listing is downloaded to the present native listing, outlined with a dot within the following instance.
scp -r -i pk_dsa.pem kali@192.168.1.112:dir .

As you’ll be able to see, the listing transference used to be achieved recursively.
Conclusion:
As you’ll be able to see, the usage of scp with a pem record is inconspicuous and simply calls for including the -i flag.
Public key authentication has professionals and cons when in comparison to password authentication.
In the primary position, generated public keys are more potent than human passwords. Contrary to password authentication, when the usage of a public key, your non-public key isn’t brought to the server (the server sends the general public key to the buyer), so it isn’t prone for Man In the Middle assaults.
Many directors select password authentication as a result of it’s simple to proportion when in comparison to key pairs.
Thank you for studying this educational explaining easy methods to use scp with a pem record; I am hoping it used to be helpful. Keep following us for extra Linux pointers and tutorials.
